前言
nmap是业内非常知名的网络扫描工具,和netcat齐名为网络瑞士军刀,想必大部分人都看过或者听说过《黑客帝国》,里面有几个场景使用的是nmap,不妨引用一张电影剧照:
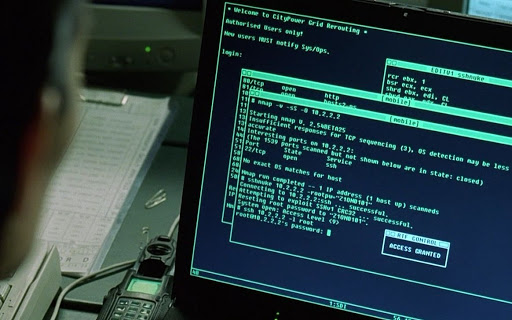
女主通过nmap扫描开放端口,并通过弱口令拿到主机权限,这不能说明nmap多么强大,因为nmap强大之处不仅仅是扫描端口,只能说明密码复杂度多么重要!nmap常用于漏洞扫描、端口扫描、网络发现等。篇幅有限,本文将从以下五大部分介绍nmap常用用法:
- 主机发现
- 网络探测
- 指纹识别与探测
- 防火墙/IDS逃逸
- 信息收集
- 暴力穷举
过程中会尽量抓包还原真实场景,用的极少的参数将尽可能忽略不讲,亦可称之为鸡肋,相信熟悉常用参数和用法后,其他鲜为人知的参数到真正需要用到的场景下再翻看man文档也不迟。
一、主机发现
涉及到的参数列表,有些参数不常用,需要时可对照参考:
| 选项 | 含义 |
|---|---|
| -sP | Ping扫描 |
| -P0 | 无Ping扫描 |
| -PS | TCP SYN Ping扫描 |
| -PU | UDP Ping扫描 |
| -PE;-PP;-PM | ICMP Ping Types扫描 |
| -PR | ARP Ping扫描 |
| -n | 禁止DNS反向解析 |
| -R | 反向解析域名 |
| –system-dns | 使用系统域名解析器 |
| -sL | 列表扫描 |
| -6 | 扫描IPv6地址 |
| –traceroute | 路由跟踪 |
| -PY | SCTP INIT Ping扫描 |
| -PA | TCP ACK Ping扫描 |
最简单的扫描,什么参数都不加,默认发SYN探测:
$ nmap 192.168.1.1
Starting Nmap 7.91 ( https://nmap.org ) at 2021-12-25 14:29 CST
Nmap scan report for openwrt.linux-code.com (192.168.1.1)
Host is up (0.00026s latency).
Not shown: 989 closed ports
PORT STATE SERVICE
21/tcp open ftp
22/tcp open ssh
53/tcp open domain
80/tcp open http
81/tcp open hosts2-ns
139/tcp open netbios-ssn
443/tcp open https
444/tcp open snpp
445/tcp open microsoft-ds
1234/tcp open hotline
5000/tcp open upnp
MAC Address: 00:0C:29:BE:5A:26 (VMware)
Nmap done: 1 IP address (1 host up) scanned in 39.51 seconds
$可以看到列出了192.168.1.1这个IP的开放端口和对应服务信息
常用指令:
nmap -sP -n 192.168.1.0/24 #列出当前网段下所有存活主机,发送ICMP探测,-n 禁止DNS反向解析,节省扫描时间
nmap -PS -n 172.16.0.0/16 #列出当前网段下所有存活主机,发送SYN Ping探测
nmap -PR -n 192.168.1.1 #使用ARP Ping扫描
nmap --system-dns 119.29.29.29 blog.linux-code.com #指定DNS地址,将域名解析成IP后再进行端口探测,不常用
nmap --traceroute -v blog.linux-code.com #路由跟踪,会列出每一跳的端口开放情况,不常用反向DNS解析:
$ nmap -R -sL 192.168.1.0/24 |& grep '('
Starting Nmap 7.91 ( https://nmap.org ) at 2021-12-25 14:33 CST
Nmap scan report for openwrt.linux-code.com (192.168.1.1)
Nmap scan report for esxi.linux-code.com (192.168.1.10)
Nmap scan report for qqdb.linux-code.com (192.168.1.84)
Nmap scan report for pan.linux-code.com (192.168.1.95)
Nmap scan report for nas.linux-code.com (192.168.1.128)
Nmap scan report for node1 (192.168.1.197)
Nmap done: 256 IP addresses (0 hosts up) scanned in 0.10 seconds
$ 二、网络探测,细致化扫描
包含的参数如下:
| 选项 | 含义 |
|---|---|
| -T | 时序选项,范围T0-T5 |
| -p|-F | 常用扫描方式 |
| -sS | TCP SYN半开扫描 |
| -sT | TCP连接扫描 |
| -sU | UDP扫描 |
| -sN;-sF;-sX | 隐蔽扫描 |
| -sA | TCP ACK扫描 |
| -sW | TCP窗口扫描 |
| -sM | TCP Maimon扫描 |
| –scanflags | 自定义TCP扫描 |
| -sI(大写字母i) | 空闲扫描 |
| -sO | IP协议扫描 |
| -b | FTP Bounce扫描 |
常用命令:
1.按时序扫描(-T0~-T5)
$ nmap -T4 192.168.1.1-T为时序扫描,分为-T0~-T5六个等级,数字越大速度越快越不精准,慢扫描多用于IDS逃逸,常用-T4;配合-F使用可提高扫描速度及效果,-F会尽量少的扫描端口,不会把默认端口全扫一遍
2.指定端口或端口范围:(-p)
$ nmap -p 80 blog.linux-code.com #只扫描80端口
$ nmap -p 80,443 -n 192.168.1.1 #80,443,-n不做DNS反解
$ nmap -p 445-1023 192.168.1.1 #445-1023
$ nmap -p 80,443,445-1000 -n 192.168.1.1 #字面意思如果既想扫TCP又想扫UDP,可以在端口前加"T:"或"U:",代表TCP和UDP,必须指定-sU(UDP扫描类型)且需要指定一个TCP扫描类型(如-sS、-sF、-sT等)
$ nmap -sU -p U:53,T:80,22 -sT -n 192.168.1.1
Starting Nmap 7.91 ( https://nmap.org ) at 2021-12-25 14:37 CST
Nmap scan report for 192.168.1.1
Host is up (0.00037s latency).
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
53/udp open|filtered domain
MAC Address: 00:0C:29:BE:5A:26 (VMware)
Nmap done: 1 IP address (1 host up) scanned in 0.53 seconds
$3.nmap的6种端口状态
- Open
- 开放状态
- Closed
- 关闭状态;当然不一定是真的关闭,不排除对方系统做了一定的安全防护从而忽略nmap的探测报文
- Filtered
- 被过滤;对方主机可能存在防火墙设备将nmap包阻隔,也可能是网络拥塞造成的,如遇到此状态建议在不同时间段再次扫描
- Unfiltered
- 未被过滤;证明端口可以访问,但无法判断是Open还是Closed,当使用ACK扫描才会呈现该状态,这时建议换一种扫描方式
- Open|Filtered
- 不确定态;可能受到专业设备的阻挡,nmap发出去的报文没有得到响应,可更换扫描方式再次尝试
- Closed|Filtered
- 不确定是关闭还是被过滤,只出现在IPID Idle扫描中,不常用
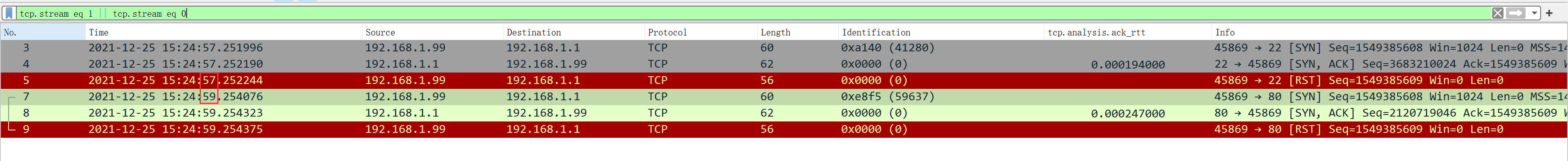
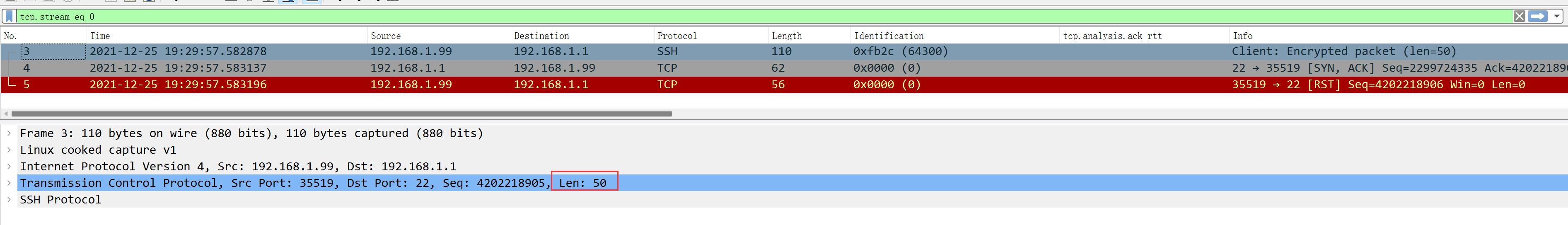
4.SYN半开扫描(-sS)
此选项常用,不会和对方主机进行三次握手,只发送SYN报文,之后断开连接,很难被防火墙或管理员检测到;结合前面所述,如果端口处于不确定态,可使用该选项进行扫描。
$ nmap -sS -p 22,80 -n 192.168.1.1
Starting Nmap 7.91 ( https://nmap.org ) at 2021-12-25 14:39 CST
Nmap scan report for 192.168.1.1
Host is up (0.00030s latency).
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
MAC Address: 00:0C:29:BE:5A:26 (VMware)
Nmap done: 1 IP address (1 host up) scanned in 0.34 seconds
$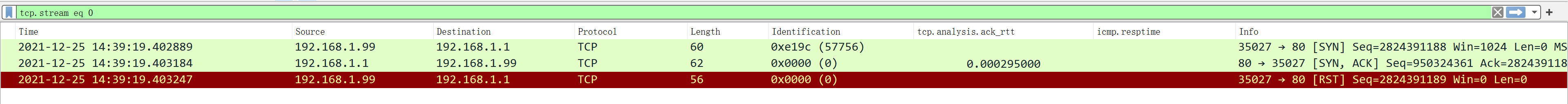
每次发完SYN后,不接受第二次握手直接RST掉对端主机的SYN包,因为从对方发送第二次握手包时nmap就已经能判断端口是否有开放。
5.TCP连接扫描(-sT)
顾名思义,建立在三次握手的基础上;当SYN半开扫描不能用的时候才考虑用它,同时也是端口扫描中最基础、最稳定的扫描方式。
$ nmap -sT -p 22,80 -n 192.168.1.1
Starting Nmap 7.91 ( https://nmap.org ) at 2021-12-25 14:43 CST
Nmap scan report for 192.168.1.1
Host is up (0.00028s latency).
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
MAC Address: 00:0C:29:BE:5A:26 (VMware)
Nmap done: 1 IP address (1 host up) scanned in 0.26 seconds
$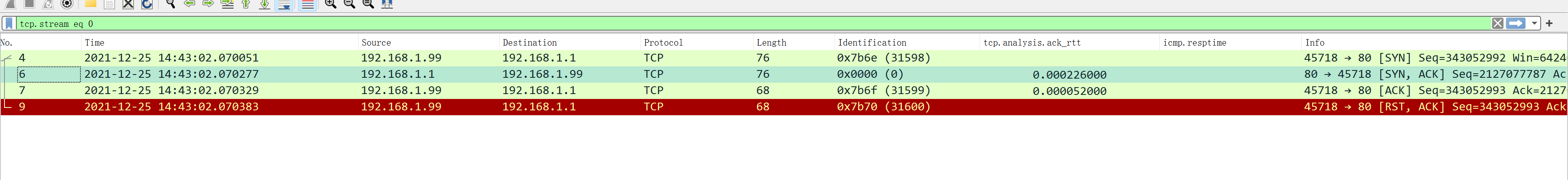
完成建联后紧接着断开连接。
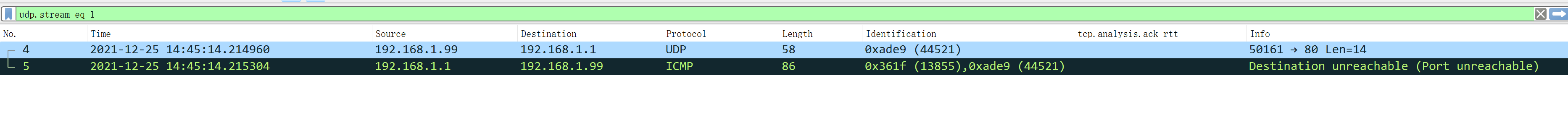
6.UDP扫描(-sU)
使用UDP报文探测,扫描速度较慢,通过ICMP不可达判断端口开放情况;以下通过-p指定端口大大缩短扫描耗时:
$ nmap -sU -p 53,80 -n 192.168.1.1
Starting Nmap 7.91 ( https://nmap.org ) at 2021-12-25 14:45 CST
Nmap scan report for 192.168.1.1
Host is up (0.00028s latency).
PORT STATE SERVICE
53/udp open|filtered domain
80/udp closed http
MAC Address: 00:0C:29:BE:5A:26 (VMware)
Nmap done: 1 IP address (1 host up) scanned in 1.52 secondss
$
7.隐蔽扫描(-sN;-sF;-sX)
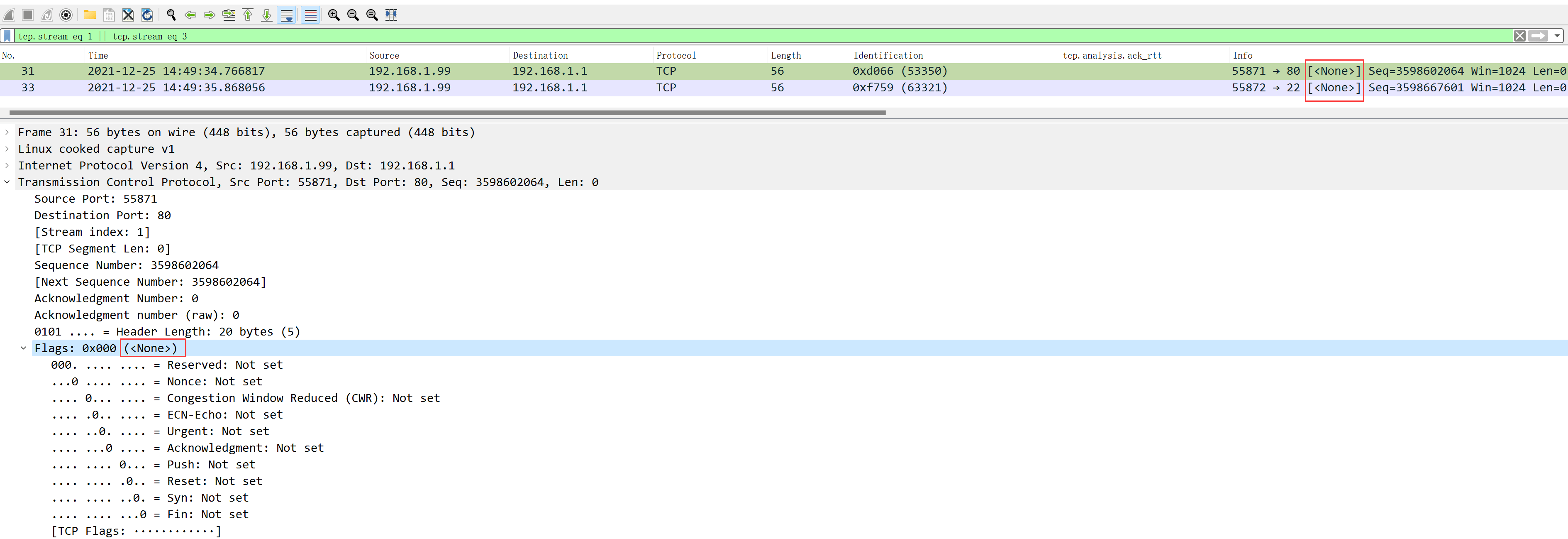
-sN为Null扫描,通过发送非常规TCP通信数据对计算机进行探测,若目标主机相应端口是关闭的,会响应一个RST数据表,若端口开放则不会响应任何信息。
$ nmap -sN -p 22,80 -n 192.168.1.1
Starting Nmap 7.91 ( https://nmap.org ) at 2021-12-25 14:49 CST
Nmap scan report for 192.168.1.1
Host is up (0.00026s latency).
PORT STATE SERVICE
22/tcp open|filtered ssh
80/tcp open|filtered http
MAC Address: 00:0C:29:BE:5A:26 (VMware)
Nmap done: 1 IP address (1 host up) scanned in 1.52 seconds
$
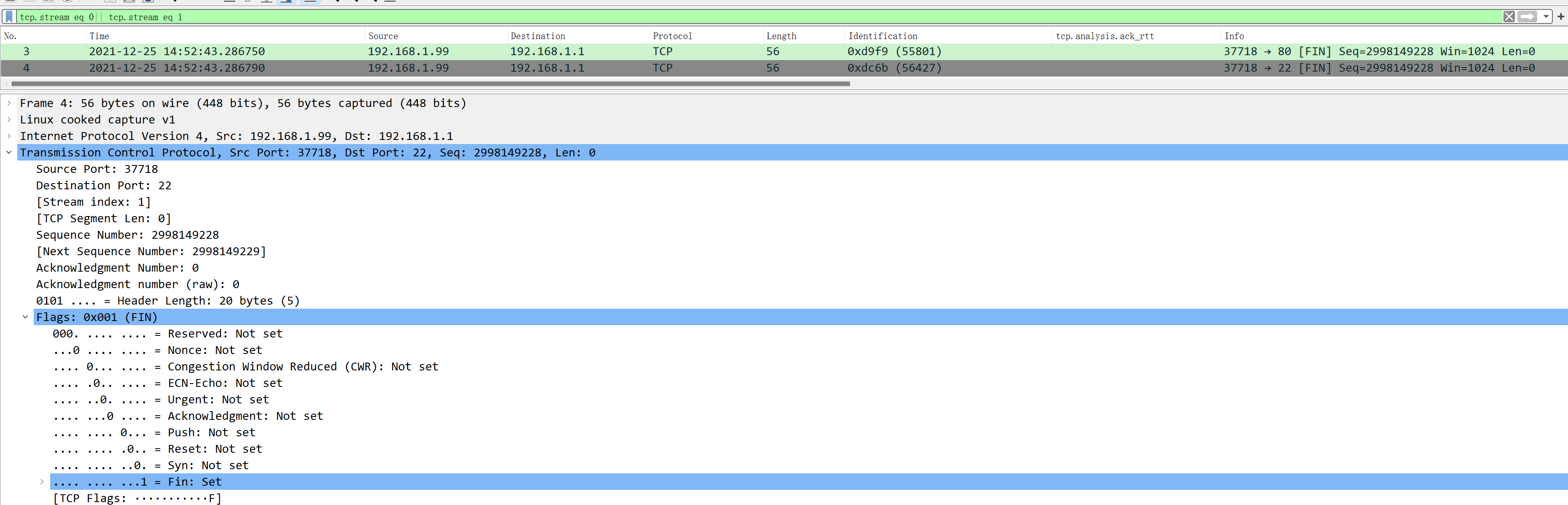
-sF为FIN扫描,不需要完成TCP握手,只向目标端口发送一个FIN包,如果收到目标响应的RST包,则说明端口开放,否则视为关闭或者被拦截的(不确定态),因为目标主机对于此类无意义请求可以选择RST也可以选择不响应。
$ nmap -sF -p 22,80 -n 192.168.1.1
Starting Nmap 7.91 ( https://nmap.org ) at 2021-12-25 14:52 CST
Nmap scan report for 192.168.1.1
Host is up (0.00024s latency).
PORT STATE SERVICE
22/tcp open|filtered ssh
80/tcp open|filtered http
MAC Address: 00:0C:29:BE:5A:26 (VMware)
Nmap done: 1 IP address (1 host up) scanned in 1.59 seconds
$
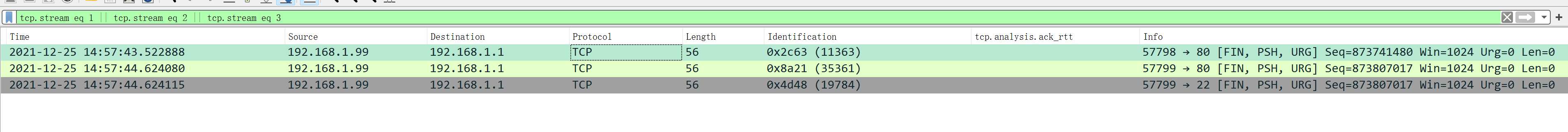
-sX为Xmas扫描,数据包的FIN、PSH和URG标志位置打开,即标志为1,如果目标主机端口开放则会响应一个RST包,否则判断位不确定态。
$ nmap -sX -p 22,80 -n 192.168.1.1
Starting Nmap 7.91 ( https://nmap.org ) at 2021-12-25 14:57 CST
Nmap scan report for 192.168.1.1
Host is up (0.00030s latency).
PORT STATE SERVICE
22/tcp open|filtered ssh
80/tcp open|filtered http
MAC Address: 00:0C:29:BE:5A:26 (VMware)
Nmap done: 1 IP address (1 host up) scanned in 1.54 seconds
$
以上三种扫描方式都会躲过一些无状态防火墙的过滤,都是通过对端的RST包来做判断,比前面提到的SYN、UDP扫描效果更好,隐蔽性大于SYN扫描。
三、指纹识别与探测
nmap通过目标指纹识别确定目标使用的系统及服务,也是信息收集中不可或缺的一部分。
| 选项 | 含义 |
|---|---|
| -sV | 版本检测 |
| –allports | 全端口扫描 |
| –version-intensity | 设置扫描强度 |
| –version-light | 轻量级扫描 |
| –version-all | 重量级扫描 |
| –version-trace | 获取详细版本信息 |
| -sR | RPC扫描 |
| -O | 操作系统扫描 |
| –osscan-limit | 对指定的目标进行OS探测 |
| –osscan-guess;–fuzzy | 推测系统版本 |
1.服务及版本探测(-sV)
-sV的最终目的并不是做端口扫描,而是通过端口判断服务类型,通过服务指纹识别出服务版本号,用的也是SYN扫描
$ nmap -sV -n 192.168.1.1
Starting Nmap 7.91 ( https://nmap.org ) at 2021-12-25 15:11 CST
Stats: 0:02:49 elapsed; 0 hosts completed (1 up), 1 undergoing Service Scan
Service scan Timing: About 81.82% done; ETC: 15:14 (0:00:29 remaining)
Nmap scan report for 192.168.1.1
Host is up (0.00025s latency).
Not shown: 989 closed ports
PORT STATE SERVICE VERSION
21/tcp open ftp vsftpd 3.0.3
22/tcp open ssh Dropbear sshd (protocol 2.0)
53/tcp open domain dnsmasq 2.81
80/tcp open http
81/tcp open hosts2-ns?
139/tcp open netbios-ssn Samba smbd 3.X - 4.X (workgroup: WORKGROUP)
443/tcp open ssl/https
444/tcp open snpp?
445/tcp open netbios-ssn Samba smbd 3.X - 4.X (workgroup: WORKGROUP)
1234/tcp open hotline?
5000/tcp open upnp MiniUPnP 2.1.20200510 (UPnP 1.1)
5 services unrecognized despite returning data. If you know the service/version, please submit the following fingerprints at https://nmap.org/cgi-bin/submit.cgi?new-service :
==============NEXT SERVICE FINGERPRINT (SUBMIT INDIVIDUALLY)==============
SF-Port80-TCP:V=7.91%I=7%D=12/25%Time=61C6C459%P=x86_64-pc-linux-gnu%r(Get
SF:Request,14F3,"HTTP/1\.0\x20403\x20Forbidden\r\nConnection:\x20close\r\n
SF:=\"viewport\"\x20/>\n\t<meta\x20name=\"format-detection\"\x20content=\"
...略
Service Info: OSs: Unix, Linux; CPE: cpe:/o:linux:linux_kernel #192.168.1.1为Openwrt,nmap识别为类Unix系统
$
常见组合用法:
$ nmap -sV -n -Pn -A 192.168.1.1 # -A操作系统探测和版本探测,还将发起traceroute等
$ nmap -sV -p 22,80 -T4 -n 192.168.1.1 #指定端口和扫描速度
$ nmap -sV --allports -n 192.168.1.12.设置扫描强度(–version-intensity)
强度范围为1-9,数字越大强度越强消耗时间越长,默认为7,而轻量级扫描--version-light相当于--version-intensity 2的快捷方式,--version-all则对应的是--version-intensity 9
$ nmap -p 80 --version-intensity 2 qq.com
Starting Nmap 7.91 ( https://nmap.org ) at 2021-12-25 15:20 CST
Nmap scan report for qq.com (183.3.226.35)
Host is up (0.0031s latency).
PORT STATE SERVICE
80/tcp open http
Nmap done: 1 IP address (1 host up) scanned in 0.35 seconds
$3.操作系统探测(-O)
nmap判断操作系统是通过指纹识别进行探测,并不是通过TTL探测,TTL值人为可以更改,因此某些场景下并不适用。
最简单的用法,直接接-O参数,不过对于IP习惯性的加上-n、-Pn,不做DNS反解,不做主机存活探测:
$ nmap -O -n -Pn 119.29.29.29
Host discovery disabled (-Pn). All addresses will be marked 'up' and scan times will be slower.
Starting Nmap 7.91 ( https://nmap.org ) at 2021-12-25 15:21 CST
Nmap scan report for 119.29.29.29
Host is up (0.0025s latency).
Not shown: 998 filtered ports
PORT STATE SERVICE
53/tcp open domain
80/tcp open http
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Aggressive OS guesses: Apple macOS 10.13 (High Sierra) - 10.15 (Catalina) or iOS 11.0 - 13.4 (Darwin 17.0.0 - 19.2.0) (91%), Apple macOS 10.14 (Mojave) (Darwin 18.2.0 - 18.6.0) (91%), Apple Mac OS X 10.11 (El Capitan) or iOS 12.4 - 13.0 (Darwin 15.6.0 - 19.0.0) (90%), Linux 4.4 (88%), Linux 2.6.18 (CentOS 5, x86_64, SMP) (86%), Apple iOS 10 (85%), Apple iOS 5.0.1 (85%), Apple iOS 5.0.1 - 5.1.1 (85%), Apple iOS 6.1.3 (85%), Apple iOS 6.0.1 (85%)
No exact OS matches for host (test conditions non-ideal).
OS detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 11.53 seconds
$4.操作系统识别(–osscan-guess;–fuzzy)
通过已有信息推测目标主机操作系统版本,此选项常用,可配合-O选项
$ nmap -O --osscan-guess -n 192.168.1.11 -Pn
Host discovery disabled (-Pn). All addresses will be marked 'up' and scan times will be slower.
Starting Nmap 7.91 ( https://nmap.org ) at 2021-12-25 15:24 CST
Nmap scan report for 192.168.1.11
Host is up (0.00020s latency).
Not shown: 996 closed ports
PORT STATE SERVICE
53/tcp open domain
1723/tcp open pptp
2000/tcp open cisco-sccp
8291/tcp open unknown
MAC Address: 00:0C:29:42:37:61 (VMware)
Device type: general purpose
Running: Linux 2.6.X|3.X
OS CPE: cpe:/o:linux:linux_kernel:2.6 cpe:/o:linux:linux_kernel:3
OS details: Linux 2.6.32 - 3.10
Network Distance: 1 hop
OS detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 2.91 seconds
$5.定时探测(–host-timeout;–scan-delay;max-scan-delay)
另外说几个比较重要的参数,可以极大程度的减少我们扫描的时间,特别是扫描整个网段的时候
$ nmap --host-timeout 10s -sS -sU -p U:53,T:443 -n 192.168.1.0/24 #每个主机最大探测时间10s,可以设置ms$ nmap --scan-delay 1s --max-scan-delay 10s -n -sV -A 192.168.1.1 #探测服务版本信息,每隔1s-10s发送一次探测包,可以有效规避限定单位时间发包量的防火墙规则$ nmap --scan-delay 2s -p 22,80 -n 192.168.1.1
Starting Nmap 7.91 ( https://nmap.org ) at 2021-12-25 15:24 CST
Nmap scan report for 192.168.1.1
Host is up (0.00024s latency).
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
MAC Address: 00:0C:29:BE:5A:26 (VMware)
Nmap done: 1 IP address (1 host up) scanned in 6.27 seconds
$仅设置--scan-delay 2s,每个包将会间隔2s才继续发下个包:
四、防火墙/IDS逃逸
包含的选项如下,这里只讲几个常用选项
| 选项 | 含义 |
|---|---|
| -f | 报文分段 |
| –mtu | 指定偏移大小 |
| -D | IP欺骗 |
| -sI | 源地址欺骗 |
| –source-port | 源端口欺骗 |
| –data-length | 指定发包长度 |
| –randomize-hosts | 目标主机随机排序 |
| –spoof-mac | MAC地址欺骗 |
1.报文分段(-f)
-f选项会将TCP头分段在几个包中,使得IDS及其它工具检测更加困难
$ nmap -f -v -p 80 -n 192.168.1.1
Starting Nmap 7.91 ( https://nmap.org ) at 2021-12-25 19:06 CST
Nmap wishes you a merry Christmas! Specify -sX for Xmas Scan (https://nmap.org/book/man-port-scanning-techniques.html).
Initiating ARP Ping Scan at 19:06
Scanning 192.168.1.1 [1 port]
Completed ARP Ping Scan at 19:06, 0.07s elapsed (1 total hosts)
Initiating SYN Stealth Scan at 19:06
Scanning 192.168.1.1 [1 port]
Discovered open port 80/tcp on 192.168.1.1
Completed SYN Stealth Scan at 19:06, 0.04s elapsed (1 total ports)
Nmap scan report for 192.168.1.1
Host is up (0.00025s latency).
PORT STATE SERVICE
80/tcp open http
MAC Address: 00:0C:29:BE:5A:26 (VMware)
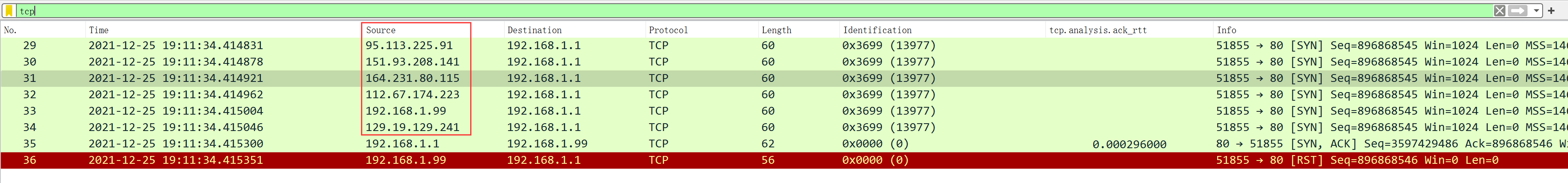
$2.IP欺骗(-D)
-D选项可以使用fake IP进行IP欺骗,使用该选项扫描对方时,会让目标主机误认为是用fake IP进行扫描,并非攻击者真实IP:
$ nmap -D RND:5 -p 80 -n 192.168.1.1 #随机使用5个IP向对端发起端口扫描
Starting Nmap 7.91 ( https://nmap.org ) at 2021-12-25 19:11 CST
Nmap scan report for 192.168.1.1
Host is up (0.00035s latency).
PORT STATE SERVICE
80/tcp open http
MAC Address: 00:0C:29:BE:5A:26 (VMware)
Nmap done: 1 IP address (1 host up) scanned in 0.38 second
$当然,其中也会包含攻击者自己的IP,起到混乱效果:
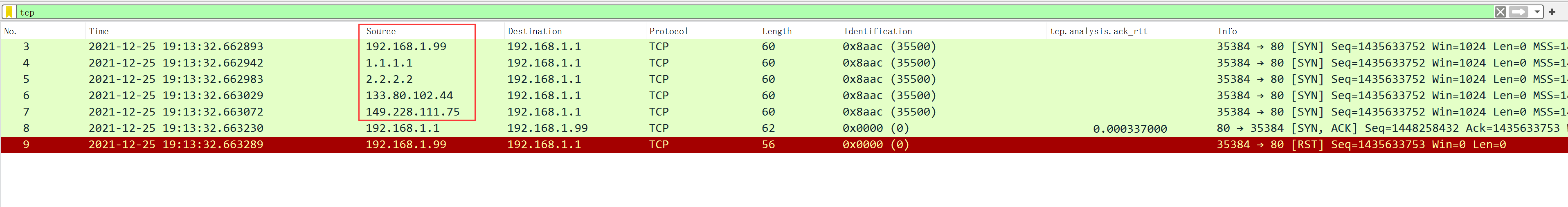
使用指定IP地址+随机IP进行端口探测:
$ nmap -D 1.1.1.1,2.2.2.2,RND:2 -p 80 -n 192.168.1.1
Starting Nmap 7.91 ( https://nmap.org ) at 2021-12-25 19:13 CST
Nmap scan report for 192.168.1.1
Host is up (0.00037s latency).
PORT STATE SERVICE
80/tcp open http
MAC Address: 00:0C:29:BE:5A:26 (VMware)
Nmap done: 1 IP address (1 host up) scanned in 0.33 seconds
$
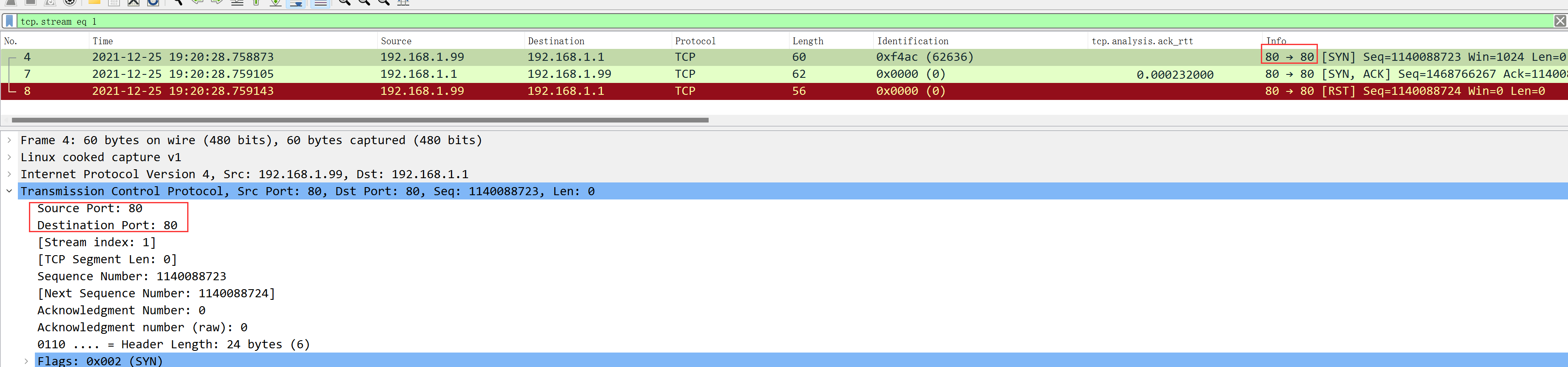
3.源端口欺骗(–source-port/-g)
指定本端源地址端口,如对方信任这些端口,则能有效规避防火墙/IDS检测:
$ nmap --source-port 80 -p 22,80 -n 192.168.1.1
Starting Nmap 7.91 ( https://nmap.org ) at 2021-12-25 19:20 CST
Nmap scan report for 192.168.1.1
Host is up (0.00025s latency).
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
MAC Address: 00:0C:29:BE:5A:26 (VMware)
Nmap done: 1 IP address (1 host up) scanned in 0.35 seconds
$
4.指定数据包大小(–data-length)
–data-length在发送报文时刻指定长度,通常情况下,TCP包是40byte,ICMP Echo是28byte,在此基础上附加任意大小的数据可达到规避防火墙效果:
$ nmap --data-length 50 -p 22 -n 192.168.1.1 #指定数据长度50字节
Starting Nmap 7.91 ( https://nmap.org ) at 2021-12-25 19:29 CST
Nmap scan report for 192.168.1.1
Host is up (0.00036s latency).
PORT STATE SERVICE
22/tcp open ssh
MAC Address: 00:0C:29:BE:5A:26 (VMware)
Nmap done: 1 IP address (1 host up) scanned in 0.34 seconds
$
5.MAC地址欺骗(–spoof-mac)
该选项可指定mac地址,也可以随机分配一个mac地址,--spoof-mac后面可以接0、Mac、Vendor Name;0表示随机生成,vendor name表示从指定厂商生成,正确的--spoof-mac参数有, Apple, 0,01:02:03:04:05:06, deadbeefcafe,0020F2, 和Cisco
$ nmap -sU -p 53 -n --spoof-mac 0 192.168.1.1
$ nmap -sS -sV -A -T4 --spoof-mac Cisco -n 192.168.1.1五、信息收集
信息收集通过调用nmap内置的lua脚本进行探测,由于nmap强项并不在于漏洞扫描,这里只列出几个常用的漏洞扫描脚本:
| 脚本 | 含义 |
|---|---|
| ip-geolocation-* | IP信息收集 |
| whois-domian/whois-ip | whois信息收集 |
| http-email-harvest | 收集E-mail信息 |
| hostmap-ip2hosts | IP反查 |
| dns-brute | DNS信息收集 |
| membase-http-info | 检索系统信息 |
| smb-security-mode | 后台打印机服务漏洞 |
| vuln | 系统漏洞扫描 |
1.whois信息收集(–script whois-domain/whois-ip)
输出篇幅过长,不贴到本篇内单独讲,可使用whois命令直接替代此功能,内置于namp的用法也很简单:
$ nmap --script whois-domain linux-code.com #查看linux-code.com的whois信息
$ nmap --script whois-ip 8.8.8.8 #查看8.8.8.8的whois信息2.dns信息收集(–script dns-brute)
枚举dns主机名,对linux-code.com进行子域名枚举:
$ nmap --script dns-brute --script-args dns-brute.domain=linux-code.com3.系统漏洞扫描(–script vuln)
nmap会调用内置脚本vuln.nse对目标主机做一次综合性的安全扫描,当然扫描强度也是局限的,有时能扫到CVE漏洞,但大部分无法实际价值;更专业的安全扫描工具建议用OpenVas、nessus等,vuln脚本相当于入门级的安全扫描。
$ nmap --script vuln -sS -n 192.168.1.1
Starting Nmap 7.91 ( https://nmap.org ) at 2021-12-25 19:32 CST
Stats: 0:04:43 elapsed; 0 hosts completed (1 up), 1 undergoing Script Scan
NSE Timing: About 99.90% done; ETC: 19:37 (0:00:00 remaining)
Nmap scan report for 192.168.1.1
Host is up (0.00022s latency).
Not shown: 989 closed ports
PORT STATE SERVICE
21/tcp open ftp
|_sslv2-drown:
22/tcp open ssh
53/tcp open domain
80/tcp open http
| http-csrf:
| Spidering limited to: maxdepth=3; maxpagecount=20; withinhost=192.168.1.1
| Found the following possible CSRF vulnerabilities:
|
| Path: http://192.168.1.1:80/
| Form id:
|_ Form action: /
|_http-dombased-xss: Couldn't find any DOM based XSS.
|_http-internal-ip-disclosure: ERROR: Script execution failed (use -d to debug)
|_http-stored-xss: Couldn't find any stored XSS vulnerabilities.
81/tcp open hosts2-ns
139/tcp open netbios-ssn
443/tcp open https
| http-csrf:
| Spidering limited to: maxdepth=3; maxpagecount=20; withinhost=192.168.1.1
| Found the following possible CSRF vulnerabilities:
|
| Path: https://192.168.1.1:443/
| Form id:
|_ Form action: /
|_http-dombased-xss: Couldn't find any DOM based XSS.
|_http-stored-xss: Couldn't find any stored XSS vulnerabilities.
|_http-vuln-cve2014-3704: ERROR: Script execution failed (use -d to debug)
|_sslv2-drown:
444/tcp open snpp
445/tcp open microsoft-ds
1234/tcp open hotline
5000/tcp open upnp
MAC Address: 00:0C:29:BE:5A:26 (VMware)
...略
Host script results:
|_samba-vuln-cve-2012-1182: NT_STATUS_OBJECT_NAME_NOT_FOUND
|_smb-vuln-ms10-054: false
|_smb-vuln-ms10-061: NT_STATUS_OBJECT_NAME_NOT_FOUND
Nmap done: 1 IP address (1 host up) scanned in 303.22 seconds
$六、暴力穷举
nmap有相当多针对服务的暴力破解脚本,你甚至可以自定义字典文件,但暴力破解这块我更倾向于使用hydra,这里只轻度提及nmap的暴力破解常见用法
| 脚本 | 含义 |
|---|---|
| mysql-brute | 破解mysql密码 |
| oracle-brute | 破解oracle密码 |
| ms-sql-brute | 破解mssql密码 |
| pgsql-brute | 破解pgsql密码 |
| http-brute | 破解http登录 |
| ftp-brute | 破解ftp密码 |
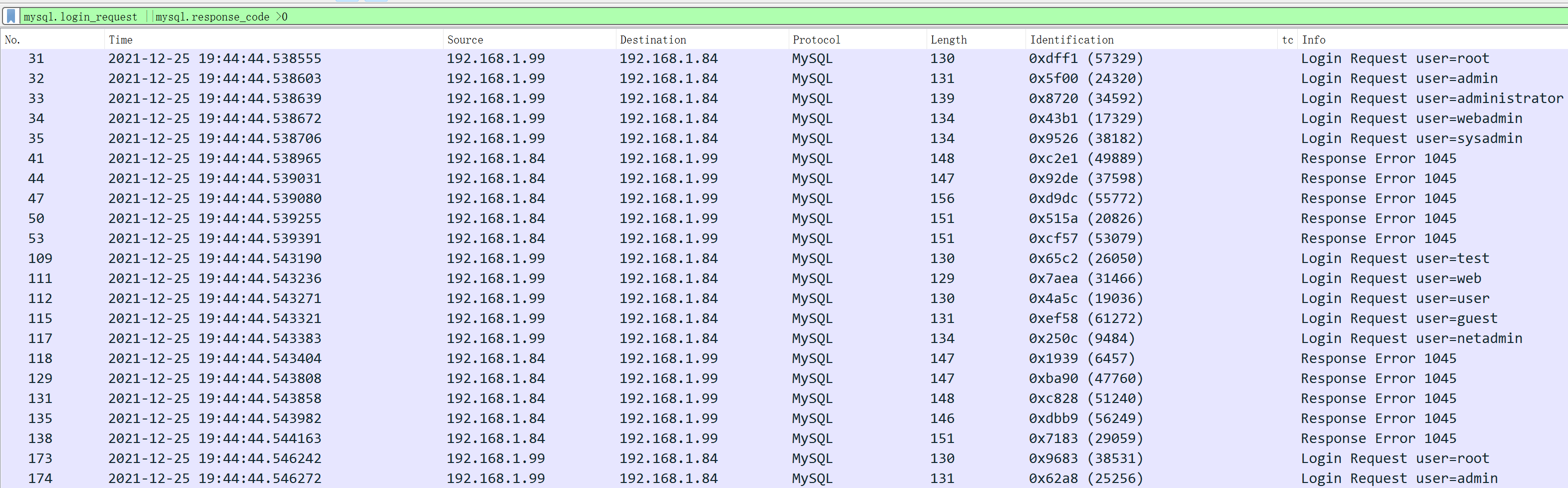
1.mysql密码破解
默认不指定字典:
$ nmap --script=mysql-brute -p3306 192.168.1.197 #如果对方数据库端口非默认,可以-p指定其他数据库同理,指定字典文件的用法,通过userdb、passsdb指定账号密码文件:
$ nmap -p 3306 --script=mysql-brute --script-args userdb=/root/user.txt --script-args passdb=/root/pass.txt -n 192.168.1.84 #习惯性加上-n不做DNS反解
Starting Nmap 7.91 ( https://nmap.org ) at 2021-12-25 19:44 CST
Nmap scan report for 192.168.1.84
Host is up (0.00027s latency).
PORT STATE SERVICE
3306/tcp open mysql
| mysql-brute:
| Accounts:
| root:123456 - Valid credentials
|_ Statistics: Performed 60 guesses in 1 seconds, average tps: 60.0
MAC Address: 00:0C:29:92:26:BB (VMware)
Nmap done: 1 IP address (1 host up) scanned in 0.97 seconds
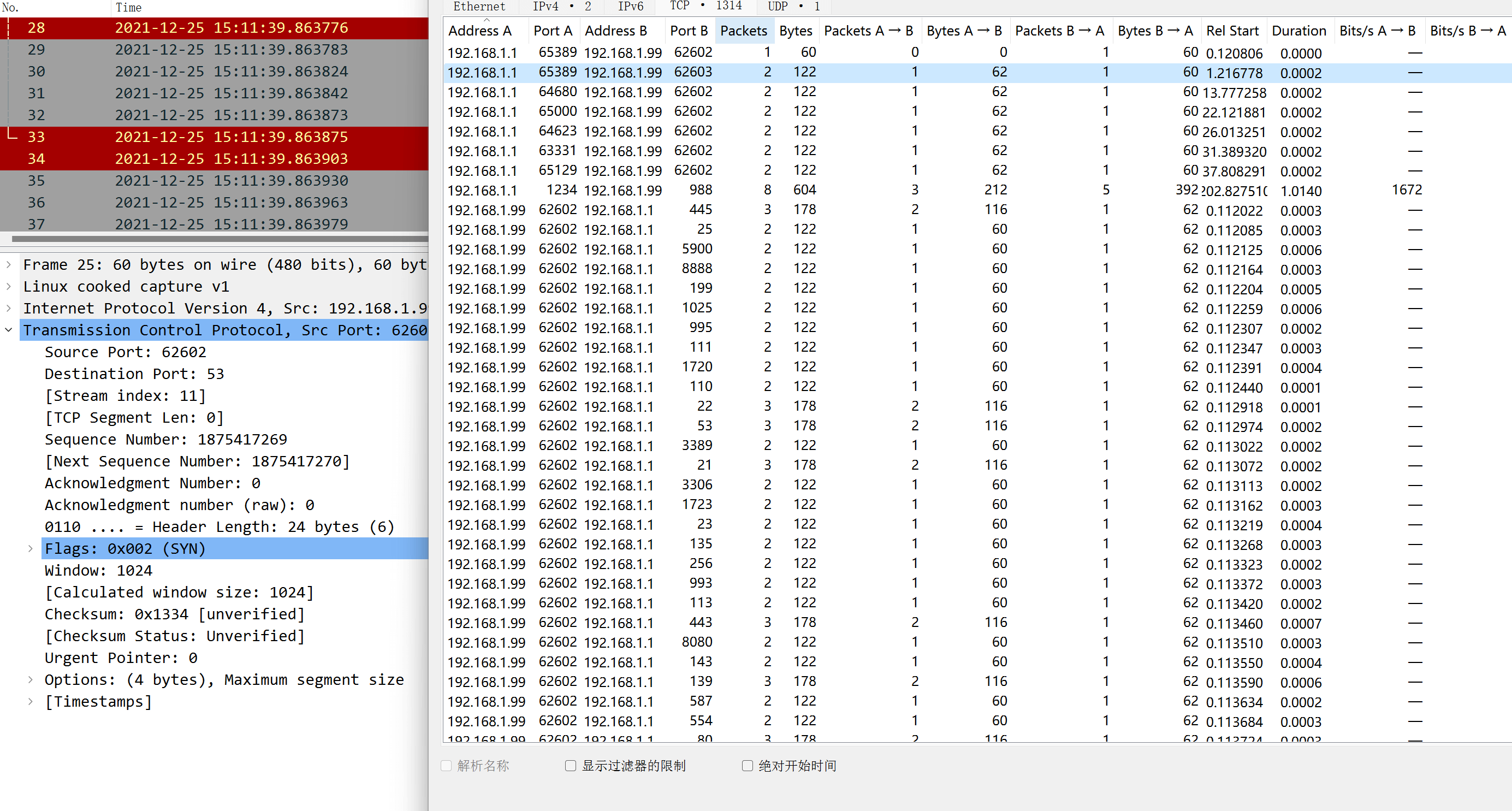
$抓包可以看到nmap不断枚举账号密码登录mysql,扫描结果将汇总成功登录的账号密码:
其他数据库一概而论,只是调用的脚本不一样,参数都是共用的,不一一列举
2.http、ftp、samba破解
和上述数据库破解同理,可以通过指定字典文件穷举登录密码:
$ nmap --script http-brute --script-args userdb=/root/user.txt,passdb=/root/pass.txt -p 82 -n 192.168.1.197
$ nmap --script ftp-brute --script-args userdb=/root/user.txt,passdb=/root/pass.txt -p 21 -n 192.168.1.197
$ nmap --script smb-brute --script-args userdb=/root/user.txt,passdb=/root/pass.txt -p 445 -n 192.168.1.1973.网段性扫描及匿名登录
nmap提供–open参数过滤只处于open状态的端口对应的主机,因此可以批量扫描整个网段某个端口开放情况:
$ nmap -p 3389 --open -n -sS 192.168.1.0/24扫描可以匿名登录的ftp主机:
$ nmap -p 21 --open -n -Pn --script=ftp-anon 192.168.1.0/24通过-oG参数可格式化输出:
$ nmap -p 3389 --open -n -sS -oG - 192.168.1.0/24 |&grep open-oX则保存为xml格式:
$ nmap -p U:53,T:80 -sU -n -sT -oX result.xml 192.168.1.0/24七、总结
nmap对于网络排错、渗透测试、网络安全领域都起着功不可没的作用,同时也饱受黑客们的青睐,技术是把双刃剑,用在哪怎么用还需使用者洁身自好。
同时附上PDF版本:
细谈网络瑞士军刀-nmap使用指南



